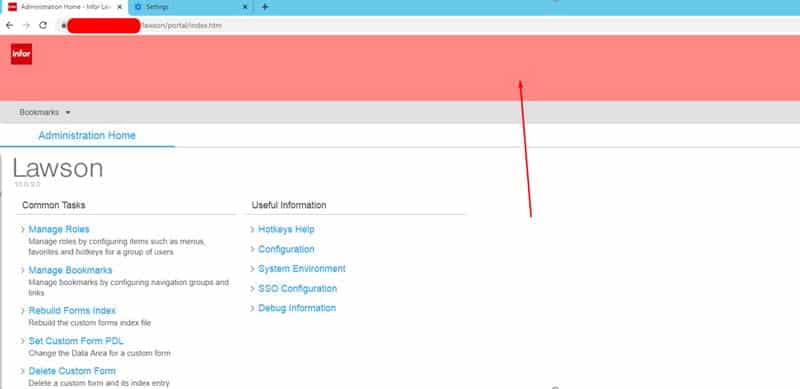
You may have saw our article on how to enable IOS DEBUG logging and realized after enabling it that the log gets spammed quite a bit which may actually make it harder to isolate an issue, especially if other users are currently in the system.
Today we will show you how to turn on DEBUG logging for a specific user to minimize log spam. This tutorial is only for the ios_logging.xml log.
- Login to your on-prem LSF system (admin rights required)
- Identify the users RM ID (case-sensitive) that you want enable debug logging for.
- Locate and backup your ios_logging.xml file in %LAWDIR%\system
- Edit ios_loggin.xml with a text editor
- Locate the following section:
<root>
<priority value=”INFO” />
<appender-ref ref=”IOS” />
<!– Appender Filters–>
<!–<appender-ref ref=”PORTAL” /> –>
<!–<appender-ref ref=”DIRECTIOS” /> –>
</root>
Change INFO to DEBUG:
<root>
<priority value=”DEBUG” />
<appender-ref ref=”IOS” />
<!– Appender Filters–>
<!–<appender-ref ref=”PORTAL” /> –>
<!–<appender-ref ref=”DIRECTIOS” /> –>
</root>
- Locate the following section:
<!– Filter for users –>
<!–
<filter class=”com.lawson.ios.util.log.Log4JMDCFilter”>
<param name=”keyToMatch” value=”username” />
<param name=”valueToMatch” value=”lawson” />
<param name=”denyOnMatch” value=”false” />
</filter>
<filter class=”org.apache.log4j.varia.DenyAllFilter”/>
–>
Uncomment this section (remove the <!– and –> characters shown in bold above) and edit the “valueToMatch” value=”lawson” replacing “lawson” with the RM Id of your user, like so:
<!– Filter for users –>
<filter class=”com.lawson.ios.util.log.Log4JMDCFilter”>
<param name=”keyToMatch” value=”username” />
<param name=”valueToMatch” value=”ENTER_USERNAME” />
<param name=”denyOnMatch” value=”false” />
</filter>
<filter class=”org.apache.log4j.varia.DenyAllFilter”/>
- Save your changes (no restart required and you should see immediate changes)
- You should now see DEBUG entries in the log for that specific user.
- Just undo step 6 to revert changes (or revert to your backup file).
Good luck and happy debugging!